Microsoft Windows Outage CrowdStrike Analysis Highlights Security Risks
Microsoft Windows Outage CrowdStrike Analysis Highlights Security Risks An unexpected IT disaster has recently affected several sectors, such as banks, airports, TV stations, and healthcare[...]

How Information Systems Significantly Helps Reduce Your Organization’s Carbon Footprint
How Information Systems Significantly Helps Reduce Your Organization’s Carbon Footprint: Practical Strategies and Benefits Reducing your organization’s carbon footprint is more important than ever, and[...]

US Government Bans Sale Of Kaspersky Software
US Government Bans Sale Of Kaspersky Software Citing Security Concerns The Biden administration has banned Kaspersky antivirus software in the United States due to concerns[...]

10 Facts You Didn’t Know About Your Average Managed IT Services Provider
10 Facts You Didn’t Know About Your Average Managed IT Services Provider: Insights for Business Owners Managed IT services providers (MSPs) are crucial in modern[...]

5 Things You Must Do When You Suspect A Hacker On Your Network
5 Things You Must Do When You Suspect A Hacker On Your Network: Quick Steps for Security Discovering a hacker on your network can be[...]

The Rising Tide of Healthcare Breaches
The Rising Tide of Healthcare Breaches: A Deep Dive into Cybersecurity Challenges In recent years, healthcare has emerged as one of the industries most targeted[...]

How To Protect Your Organization For Cyber Breaches When Employees Are Terminated
How To Protect Your Organization For Cyber Breaches When Employees Are Terminated: Best Practices and Strategies When an employee leaves your organization, ensuring they no[...]

NIST Cybersecurity Framework 2.0
NIST Cybersecurity Framework 2.0: Essential Steps for Small Business Success Are you a small business looking to strengthen your cybersecurity? The NIST Cybersecurity Framework 2.0:[...]

Ethical vs. Unethical Use Of Artificial Intelligence In Cybersecurity
Ethical vs. Unethical Use Of Artificial Intelligence In Cybersecurity: A Critical Analysis As the digital world continues to evolve, the role of artificial intelligence (AI)[...]

How Artificial Intelligence Can Help Organizations With Inventory Management
How Artificial Intelligence Can Help Organizations With Inventory Management: Boost Efficiency and Accuracy Artificial intelligence (AI) is transforming the way organizations manage their inventory. AI[...]
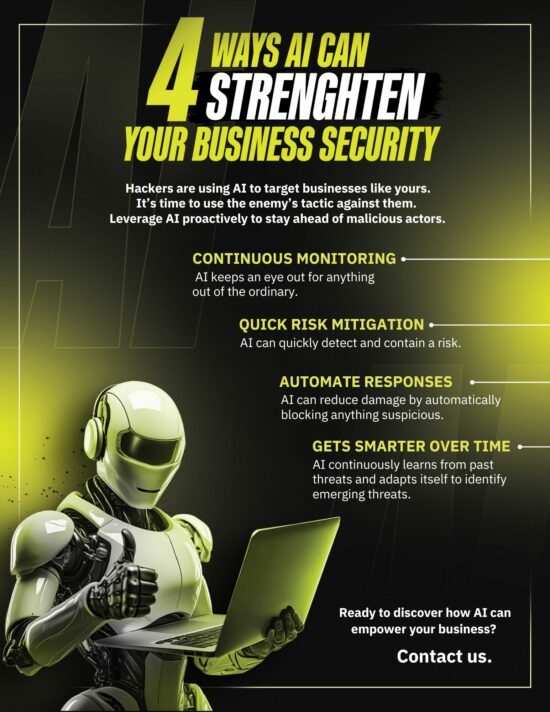
4 Ways Artificial Intelligence Can Strengthen Business Security
4 Ways Artificial Intelligence Can Strengthen Business Security: Enhancing Protection and Efficiency In today’s digital age, businesses face growing cybersecurity threats. Protecting sensitive data and[...]

5 Ways Artificial Intelligence Technology Can Help Small Business Succeed
5 Ways AI Technology Can Help Small Business Succeed Artificial Intelligence (AI) is not just for big corporations anymore; it’s also becoming a powerful tool[...]